In the digital era, data has become one of the most valuable assets for enterprises. From customer information and financial records to intellectual property and operational insights, data drives decision-making and competitive advantage. As a result, Data Protection is no longer just an IT concern—it is a critical component of enterprise operations and long-term business sustainability.
This article explores why Data Protection plays a central role in modern enterprises, the risks of neglecting it, and how organizations can build resilient data protection strategies to support growth and trust.
The Growing Importance of Data in Enterprise Operations
Data as a Strategic Business Asset
Enterprises rely heavily on data to optimize processes, personalize customer experiences, and forecast future trends. As data volumes increase, so does the responsibility to manage and protect it effectively.
A single data breach can disrupt operations, damage customer trust, and result in severe financial and legal consequences. That is why Data Protection must be embedded into daily operations rather than treated as a secondary technical task.

Increasing Threats in a Connected World
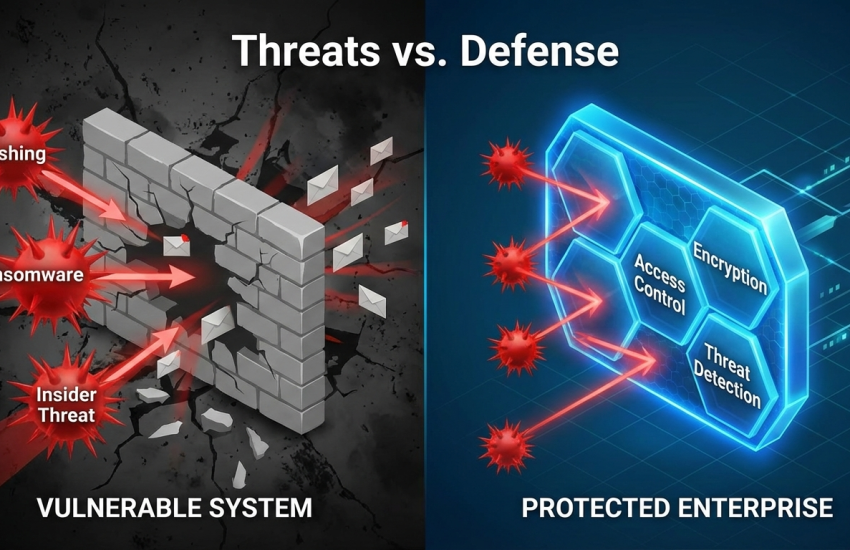
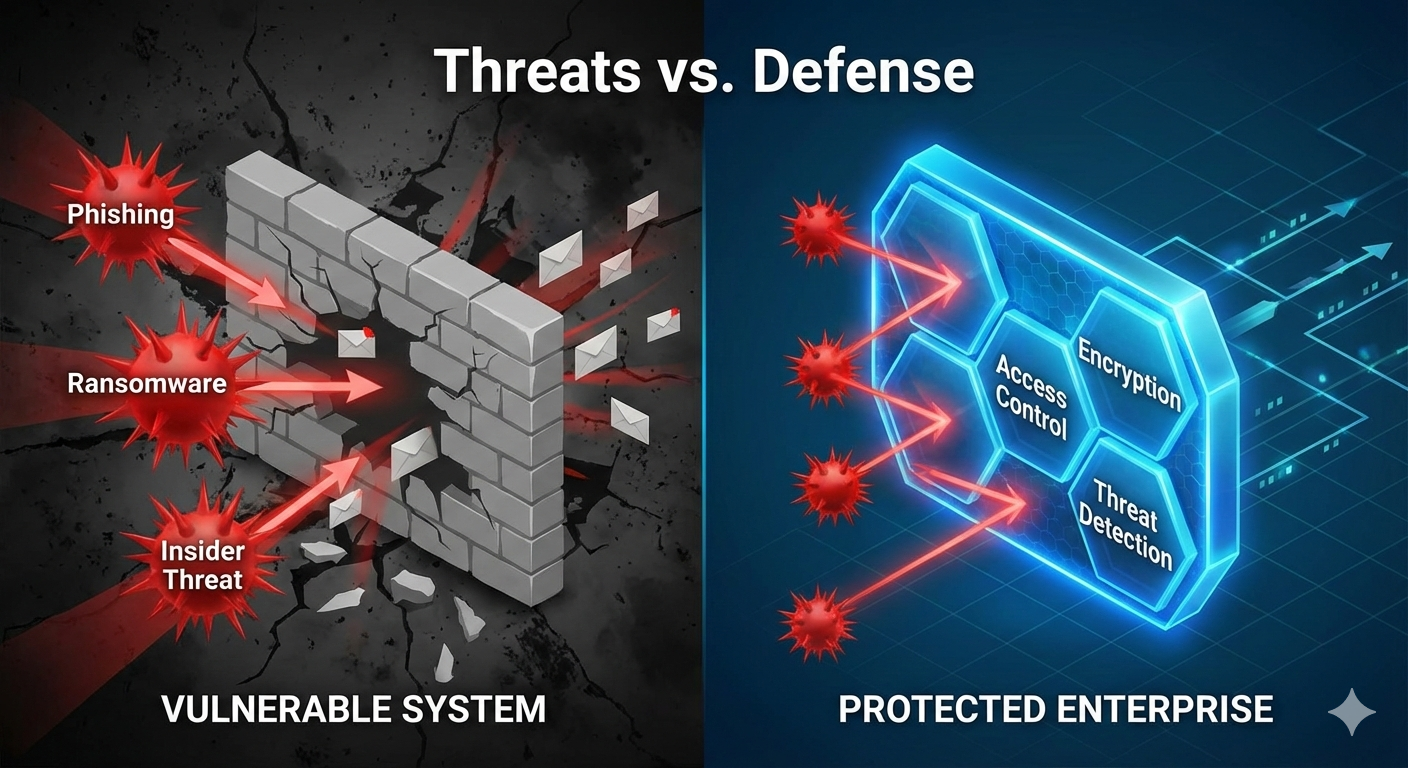
Cyber threats are becoming more sophisticated, targeting enterprises of all sizes. Phishing attacks, ransomware, insider threats, and system vulnerabilities expose sensitive data to unauthorized access.
Without a strong Data Protection framework, enterprises risk not only losing data but also facing operational downtime that directly impacts revenue and brand reputation.
Many of these data-related threats are part of broader security challenges enterprises face as they digitize operations and scale. These enterprise-level issues are explored further in Enterprise Security Challenges Businesses Are Facing Today
What Data Protection Means for Enterprises
Beyond Basic Security Measures
Data Protection goes far beyond firewalls and antivirus software. It encompasses a comprehensive approach that includes data encryption, access control, backup and recovery, and governance policies.
Effective Data Protection ensures that data is:
- Confidential: accessible only to authorized users
- Integral: protected from unauthorized modification
- Available: accessible when needed for operations
Data Protection Across the Data Lifecycle
Enterprise data moves through multiple stages—from creation and storage to processing, sharing, and archiving. Each stage introduces potential risks.
A robust Data Protection strategy addresses security and compliance across the entire data lifecycle, ensuring consistent protection regardless of where or how the data is used.
Regulatory Compliance and Legal Responsibility
Meeting Global and Industry Regulations
Enterprises are subject to increasingly strict data privacy and protection regulations, such as GDPR and other regional or industry-specific frameworks. Failure to comply can result in heavy fines and legal actions.
Data Protection helps organizations:
- Demonstrate regulatory compliance
- Reduce legal exposure
- Maintain transparency and accountability
This regulatory pressure has made Data Protection a board-level concern rather than a purely technical issue.

Protecting Customer and Partner Trust
Trust is a critical currency in enterprise relationships. Customers and business partners expect organizations to safeguard their data responsibly.
Technology-driven enterprises working with partners like AMADEUS TECHNOLOGY B.V. often prioritize Data Protection as a key differentiator, signaling reliability and professionalism in the market.
Operational Resilience Through Data Protection
Minimizing Business Disruption
Operational continuity depends heavily on data availability. Data loss due to cyber incidents, system failures, or human error can bring operations to a halt.
Data Protection strategies such as regular backups, disaster recovery planning, and redundancy ensure that enterprises can recover quickly and maintain service continuity.
Strong Data Protection depends on systems that are designed to be both secure and resilient from the start. This architectural perspective is discussed in Building Secure and Scalable Systems for Long-Term Business Growth
Supporting Digital Transformation
As enterprises adopt cloud services, remote work models, and data-driven platforms, the attack surface expands. Without strong Data Protection practices, digital transformation efforts can increase risk instead of reducing it.
Well-designed Data Protection frameworks enable enterprises to innovate confidently while keeping sensitive information secure.

Common Data Protection Challenges for Enterprises
Fragmented Systems and Data Silos
Many enterprises operate with legacy systems and multiple data repositories. This fragmentation makes it difficult to enforce consistent Data Protection policies across the organization.
Centralized governance and integrated security controls are essential to overcome these challenges.
Human Error and Insider Risks
Not all data breaches come from external attackers. Misconfigured systems, weak passwords, and accidental data sharing by employees remain major risks.
Effective Data Protection includes employee training, clear policies, and role-based access controls to reduce human-related vulnerabilities.
Best Practices for Enterprise Data Protection
Embed Data Protection into System Design
Data Protection should be built into systems from the design phase, not added later. This includes secure architectures, least-privilege access models, and encryption by default.
Enterprises that adopt this approach early benefit from stronger security and lower long-term costs.
Partner with Experienced Technology Providers
Implementing enterprise-grade Data Protection requires both technical expertise and strategic insight. Working with experienced partners such as AMADEUS TECHNOLOGY B.V. helps organizations align Data Protection initiatives with broader business goals.
These partnerships ensure that security solutions scale with the enterprise and adapt to evolving threats.
Continuously Monitor and Improve
Threat landscapes and regulatory requirements change constantly. Enterprises must regularly review, test, and update their Data Protection strategies to remain effective.
Ongoing monitoring, audits, and incident response planning are essential for maintaining strong protection over time.
Data Protection as a Core Pillar of Enterprise Operations
In today’s data-driven economy, enterprises cannot separate operational success from Data Protection. It underpins business continuity, regulatory compliance, customer trust, and long-term growth.
By treating Data Protection as a strategic priority rather than a technical afterthought, enterprises build stronger, more resilient operations. Organizations that invest in robust frameworks—often with guidance from experts like AMADEUS TECHNOLOGY B.V.—are better positioned to thrive in an increasingly complex digital landscape.