In an increasingly digital and interconnected environment, enterprise security has become a top concern for organizations of all sizes. As businesses expand their digital operations, adopt cloud platforms, and rely more heavily on data-driven systems, security risks grow in both scale and complexity. Today’s enterprises must address not only technical vulnerabilities but also organizational and management-related challenges that directly impact security.
Understanding these challenges is essential for building resilient security strategies, especially as many organizations adopt Technology-Based Management Models to manage operations, data, and decision-making.

The Expanding Enterprise Attack Surface
Digital Transformation and System Complexity
Modern enterprises operate across cloud platforms, remote work environments, third-party integrations, and mobile devices. Each additional system increases the attack surface, creating new opportunities for cyber threats.
While digital transformation enables efficiency and scalability, it also introduces security gaps if systems are not properly governed. Enterprises using Technology-Based Management Models must ensure that security is embedded across all digital layers, not added as an afterthought.
Shadow IT and Uncontrolled Tools
Employees often adopt tools and applications without formal approval to increase productivity. While well-intentioned, this practice—known as shadow IT—creates blind spots in enterprise security.
Without centralized oversight, these tools may lack proper access controls, encryption, or compliance measures.

Data Protection and Information Security Risks
Growing Volume of Sensitive Data
Enterprises manage vast amounts of sensitive data, including customer information, financial records, and intellectual property. As data volumes grow, so does the challenge of protecting it consistently across systems.
Data breaches can lead to regulatory penalties, reputational damage, and long-term loss of trust. Enterprises must align data protection practices with their broader Technology-Based Management Models to maintain visibility and control.
Many of these enterprise-level challenges originate from fundamental threats that affect organizations at all stages of growth. A deeper look at these issues—including phishing, ransomware, weak access controls, and data exposure—is explored in Cybersecurity Risks Every Growing Business Should Be Aware Of
Inconsistent Data Governance
Many organizations struggle with fragmented data governance. Different departments may apply different security standards, leading to inconsistent protection and increased risk.
Effective data governance requires unified policies, centralized monitoring, and clear accountability structures.

Identity and Access Management Challenges
Managing Access at Scale
As enterprises grow, managing user identities and access permissions becomes increasingly complex. Employees, contractors, and partners often require different levels of access across multiple systems.
Without strong identity and access management (IAM), organizations face risks such as privilege creep, unauthorized access, and insider threats.
Balancing Security and Usability
Overly restrictive access controls can reduce productivity, while weak controls expose systems to attack. Enterprises must strike a balance by implementing role-based access and continuous authentication models.
Human Factors and Organizational Risks
Lack of Security Awareness
Human error remains one of the leading causes of security incidents. Phishing attacks, weak passwords, and poor data handling practices continue to affect enterprises.
Even the most advanced security technologies are ineffective if employees are not trained to recognize threats and follow security policies.
Misalignment Between Security and Management
In many organizations, security initiatives operate separately from management strategy. This misalignment leads to inconsistent enforcement, unclear ownership, and reactive security responses.
Enterprises adopting Technology-Based Management Models should integrate security metrics, risk assessments, and compliance tracking into management systems to ensure alignment.
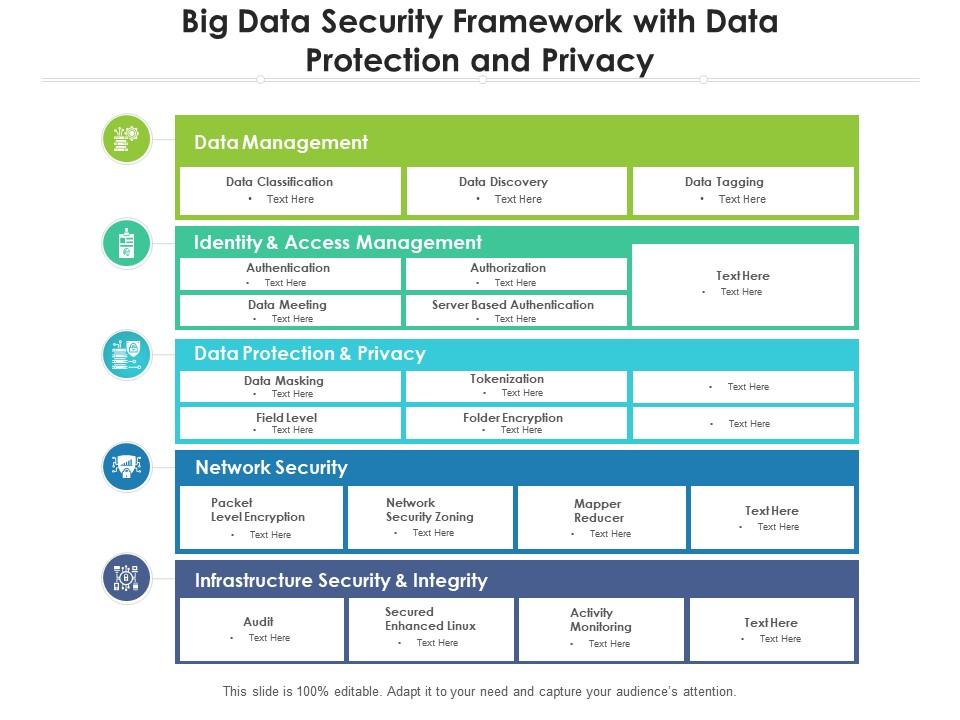
Technology and Infrastructure Challenges
Legacy Systems and Technical Debt
Many enterprises still rely on legacy systems that were not designed to meet modern security requirements. These systems may lack encryption, regular updates, or integration capabilities.
Replacing or securing legacy infrastructure is often complex and costly, but ignoring it increases long-term risk.
Cloud Security Misconfigurations
Cloud platforms offer scalability and flexibility, but misconfigured environments remain a major source of enterprise security incidents. Incorrect permissions, exposed storage, and lack of monitoring are common issues.
Enterprises must treat cloud security as a shared responsibility and ensure internal teams understand their role.
Compliance and Regulatory Pressure
Increasing Regulatory Complexity
Enterprises operate under growing regulatory requirements related to data protection, privacy, and operational resilience. Failing to meet compliance standards can result in fines and legal action.
Security strategies must align with regulatory obligations and be supported by clear documentation and audit trails.
Continuous Compliance Challenges
Compliance is not a one-time effort. Enterprises must continuously monitor systems, policies, and controls to remain compliant as regulations evolve.
Addressing Enterprise Security Challenges Effectively
Embedding Security into Management Models
Security should be an integral part of Technology-Based Management Models, not a standalone function. This includes:
- Integrating security KPIs into management dashboards
- Aligning security policies with operational workflows
- Using centralized systems for monitoring and reporting
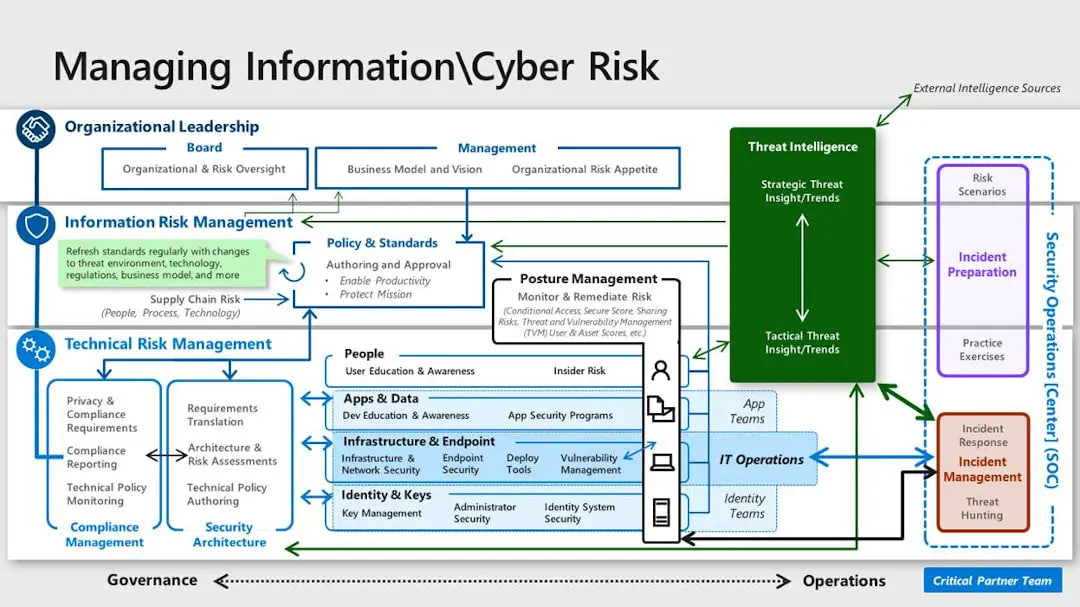
Adopting a Risk-Based Approach
Enterprises should prioritize security investments based on risk impact rather than attempting to address every threat equally. Risk-based frameworks improve resource allocation and decision-making.
Strengthening Collaboration Across Teams
Security, IT, and management teams must collaborate closely. Clear communication and shared responsibility improve response times and reduce gaps.
Enterprise Security as a Strategic Management Challenge
Enterprise security is no longer just a technical issue—it is a strategic management challenge. As organizations adopt digital tools and Technology-Based Management Models, security must evolve alongside management practices, governance structures, and decision-making processes.
Enterprises that proactively address security challenges by aligning technology, people, and management are better positioned to protect their assets, maintain trust, and sustain long-term growth. In today’s digital landscape, strong enterprise security is not only about defense—it is about enabling confident and resilient business operations.

